Internet is now the basic need of our daily life. With the increasing use of smartphones, most of the things are now online. Every time we have to do something, we just use our smartphone or desktop. This is the reason wi-fi hotspots can be found everywhere.
People also use wireless in their home network to connect all devices. Every person can see the neighborhood wi-fi networks in the system, and they want to use it for free. But most these networks are secured with a password key. You need to know this security key to access the network. When your own network is down, you will desperately want to connect to these neighborhood networks. For this, people generally search for wi-fi password cracking tools to get unauthorized access to those wireless networks.
Sometimes when you are on a network, you also want to check what is happening on the network. This happens mostly in big organizations, when an employer wants to check who is doing what in the network. For these things, there are a few network hacking tools available that let users analyze packets and see what other users are doing.
Wireless Networks and Hacking
Wireless networks are based on IEEE 802.11 standards defined by IEEE(Institute of Electrical and Electronics Engineers) for ad hoc networks or infrastructure networks. Infrastructure networks have one or more access points which coordinate the traffic between the nodes. But in ad hoc networks, there is no access point; each node connects in a peer-to-peer way.
Basically there are two types of vulnerabilities which can be found in the Wireless LAN. One is poor configuration and the other is poor encryption. Poor configuration is caused by the network admin who manages the network. It may include the weak password, no security settings, use of default configurations, and other user related things. Poor encryption is related to security keys used to protect the wireless network. It is there because of issues in WEP or WPA.
Using these WiFi hacking gadgets you are able to kick people off their network, perform evil twin or Man in the Middle attacks.
Top 5 WiFi Hacking Gadgets
1. WiFi Pineapple

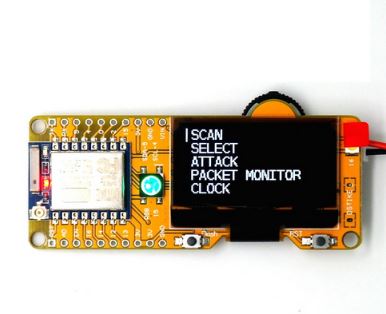
2. WiFi Deauther OLED or Wristband

3. WiFi Duck

4. Crazy Radio PA2

5. Cactus WHID – WiFi Keylogger & Rubber Ducky


We personally recommend using all the above mentioned wifi hacking gadgets as they each have their own unique attack vectors for any assessment. If you think we missed a crucial hacking gadget let us know in the comment section below.